OpenWebUI
Resource Information
| Name | IP Address | Details |
|---|---|---|
| Azure Resource Group | - | CPD-DEV-OpenWebUI |
| nginx | 10.50.1.15 | LinuxOS in Azure running nginx |
| openwebuiprod | 10.50.7.4/5 | PROD Container Instance |
| openwebuidev | 10.50.6.4/5 | DEV Container Instance |
| openwebui-recoveryservicesvault | - | Responsible to store snapshots of the kmgopenwebui-data vault file shares |
| kmgopenwebui-data | - | Storage Account |
| openwebuiprod.json Deployment Template | - | Download |
| openwebuidev.json Deployment Template | - | Download |
Container Deployment Template
warning
Changing hardware resources like CPU or RAM requires to delete the current machine running the container instances.
Test Container Template
1{
2 "$schema": "https://schema.management.azure.com/schemas/2019-04-01/deploymentTemplate.json#",
3 "contentVersion": "1.0.0.0",
4 "resources": [
5 {
6 "type": "Microsoft.ContainerInstance/containerGroups",
7 "apiVersion": "2021-09-01",
8 "name": "openwebuidev",
9 "location": "westeurope",
10 "properties": {
11 "containers": [
12 {
13 "name": "openwebuidev",
14 "properties": {
15 "image": "ghcr.io/open-webui/open-webui:v0.8.8",
16 "resources": {
17 "requests": {
18 "cpu": 1.0,
19 "memoryInGb": 1.0
20 }
21 },
22 "ports": [
23 {
24 "port": 80
25 },
26 {
27 "port": 3000
28 },
29 {
30 "port": 8080
31 }
32 ],
33 "environmentVariables": [
34 {
35 "name": "WEBUI_URL",
36 "value": "https://chat-dev.keesing.ai/"
37 },
38 {
39 "name": "ENABLE_OAUTH_SIGNUP",
40 "value": "true"
41 },
42 {
43 "name": "OAUTH_UPDATE_PICTURE_ON_LOGIN",
44 "value": "true"
45 },
46 {
47 "name": "MICROSOFT_CLIENT_ID",
48 "secureValue": "eedc8891-abba-4020-bbb8-7b62ea8930c7"
49 },
50 {
51 "name": "MICROSOFT_CLIENT_SECRET",
52 "secureValue": "ARs8Q~Wg76nuxx6R_pdsB.y4qE8o-h3SH81h8ad6"
53 },
54 {
55 "name": "MICROSOFT_CLIENT_TENANT_ID",
56 "secureValue": "3d93d201-da81-4616-a595-bb0c944ca828"
57 },
58 {
59 "name": "MICROSOFT_REDIRECT_URI",
60 "value": "https://chat-dev.keesing.ai/oauth/microsoft/callback"
61 },
62 {
63 "name": "OPENID_PROVIDER_URL",
64 "value": "https://login.microsoftonline.com/3d93d201-da81-4616-a595-bb0c944ca828/v2.0/.well-known/openid-configuration"
65 },
66 {
67 "name": "WEBUI_AUTH_SIGNOUT_REDIRECT_URL",
68 "value": "https://chat-dev.keesing.ai/auth"
69 }
70 ],
71 "volumeMounts": [
72 {
73 "name": "openwebuivolumedev",
74 "mountPath": "/app/backend/data"
75 }
76 ]
77 }
78 }
79 ],
80 "osType": "Linux",
81 "ipAddress": {
82 "type": "Private",
83 "ip": "10.30.6.10",
84 "ports": [
85 {
86 "protocol": "tcp",
87 "port": 80
88 },
89 {
90 "protocol": "tcp",
91 "port": 3000
92 },
93 {
94 "protocol": "tcp",
95 "port": 8080
96 }
97 ]
98 },
99 "volumes": [
100 {
101 "name": "openwebuivolumedev",
102 "azureFile": {
103 "shareName": "openwebuidatadev",
104 "storageAccountName": "kmgopenwebuidata",
105 "storageAccountKey": "sOKVp6gu2IjS2zMaZkUNKjsUQMq46wlGH3gW98zx33amrKERyZaLGCxLhqg8MAZohsgkI9NFk582+AStJnFHBA=="
106 }
107 }
108 ],
109 "subnetIds": [
110 {
111 "id": "/subscriptions/c192f809-f6a4-4462-969a-00ddb9ba8354/resourceGroups/KMG_Resource_Group/providers/Microsoft.Network/virtualNetworks/KMG_Azure_Network/subnets/openwebui-dev-subnet"
112 }
113 ]
114 }
115 }
116]
117}Nginx
Nginx Configuration
warning
Always Restart nginX service after making changes, to take effect.
sudo systemctl restart nginx
info
Details
/etc/nginx/conf.d/openwebui.conf
server {
listen 443 ssl;
http2 on;
server_name chat.keesing.ai;
# Cloudflare Origin Certificate (ΜΟΝΟ για Cloudflare->Origin)
# ssl_certificate /etc/ssl/internal/chat.keesing.ai.crt;
# ssl_certificate_key /etc/ssl/internal/chat.keesing.ai.key;
# ssl_certificate /etc/ssl/cloudflare/origin.crt;
# ssl_certificate_key /etc/ssl/cloudflare/origin.key;
ssl_certificate /etc/letsencrypt/live/keesing.ai/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/keesing.ai/privkey.pem;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers HIGH:!aNULL:!MD5;
# Increase if large files are being transferred
client_max_body_size 50m;
location / {
# === PUT INTERNAL IP HERE ===
# π.χ. http://127.0.0.1:8080 ή http://192.168.1.100:8080
proxy_pass http://10.50.3.5:8080;
# WebSockets/HTTP1.1
proxy_http_version 1.1;
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection "upgrade";
# Forwarded headers
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
# Timeouts/Buffering
proxy_read_timeout 3600s;
proxy_send_timeout 3600s;
proxy_buffers 64 32k;
proxy_busy_buffers_size 64k;
}
}
# HTTP → HTTPS redirect
server {
listen 80;
server_name chat.keesing.ai;
return 301 https://$host$request_uri;
}
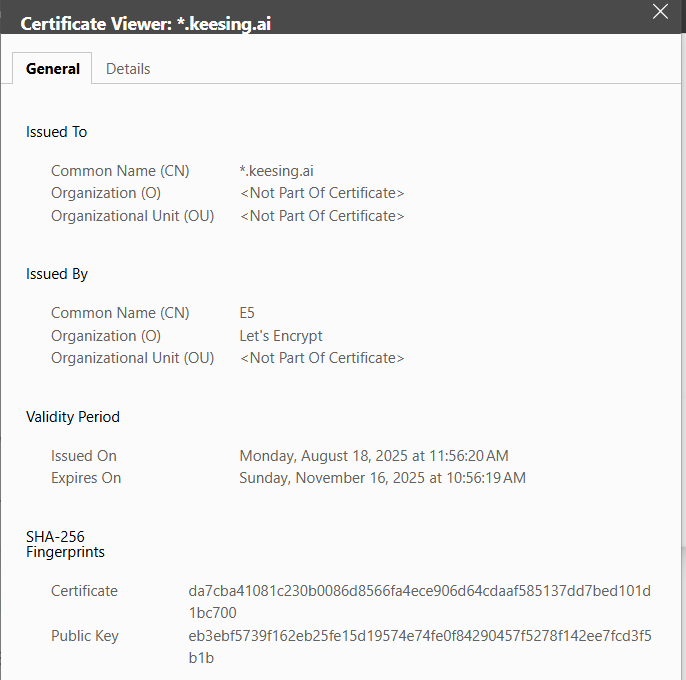
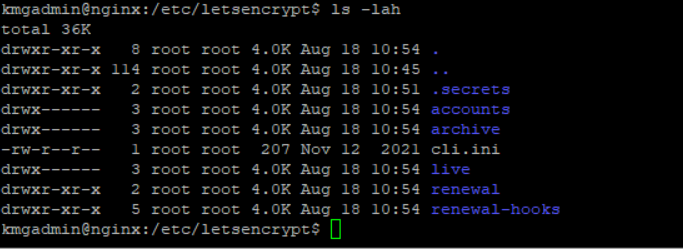
SSL Certificates
Certbot is running on the nginx machine(10.50.1.15/24).
Certbot | Manual Configuration
info
Details
Run Certbot
kmgadmin@nginx:/etc/letsencrypt$ sudo certbot certonly \
--dns-cloudflare \
--dns-cloudflare-credentials /etc/letsencrypt/.secrets/cloudflare.ini \
-d "*.keesing.ai" -d "keesing.ai" \
--agree-tos --email ict-amsterdam@keesing.com --non-interactive
Saving debug log to /var/log/letsencrypt/letsencrypt.log
Account registered.
Requesting a certificate for *.keesing.ai and keesing.ai
Waiting 10 seconds for DNS changes to propagate
Successfully received certificate.
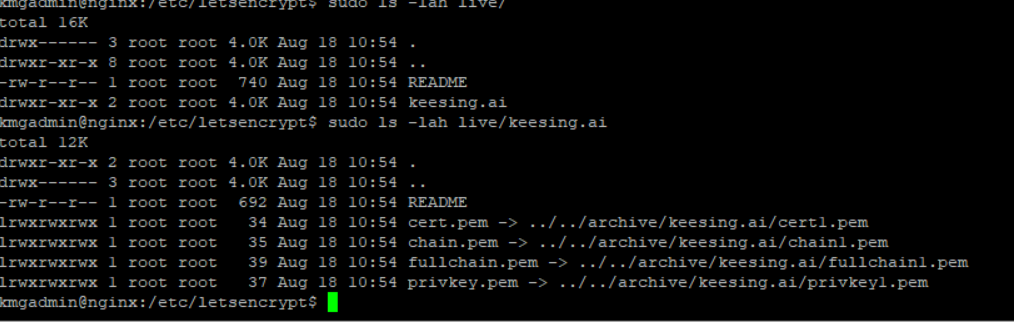
Certificate is saved at: /etc/letsencrypt/live/keesing.ai/fullchain.pem
Key is saved at: /etc/letsencrypt/live/keesing.ai/privkey.pem
This certificate expires on 2025-11-16.
These files will be updated when the certificate renews.
Certbot has set up a scheduled task to automatically renew this certificate in the background.
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
If you like Certbot, please consider supporting our work by:
* Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate
* Donating to EFF: https://eff.org/donate-le
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Show Certificates
info
kmgadmin@nginx:~$ sudo certbot certificates
Saving debug log to /var/log/letsencrypt/letsencrypt.log
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Found the following certs:
Certificate Name: keesing.ai
Serial Number: 57d171c7c123ab57312a81b033d533966e8
Key Type: ECDSA
Domains: *.keesing.ai keesing.ai
Expiry Date: 2025-11-16 09:56:19+00:00 (VALID: 89 days)
Certificate Path: /etc/letsencrypt/live/keesing.ai/fullchain.pem
Private Key Path: /etc/letsencrypt/live/keesing.ai/privkey.pem
- - - - - -
Certbot Timers and Schedules
info
Details
systemctl list-timers | grep certbot
kmgadmin@nginx:~$ systemctl list-timers | grep certbot
Mon 2025-08-18 18:46:11 UTC 7h -
- certbot.timer certbot.service
kmgadmin@nginx:~$ systemctl status certbot.timer
● certbot.timer - Run certbot twice daily
Loaded: loaded (/usr/lib/systemd/system/certbot.timer; enabled; preset: enabled)
Active: active (waiting) since Mon 2025-08-18 10:46:03 UTC; 51min ago
Trigger: Mon 2025-08-18 18:46:11 UTC; 7h left
Triggers: ● certbot.service
Aug 18 10:46:03 nginx systemd[1]: Started certbot.timer - Run certbot twice daily.
kmgadmin@nginx:~$ systemctl status certbot.service
○ certbot.service - Certbot
Loaded: loaded (/usr/lib/systemd/system/certbot.service; static)
Active: inactive (dead)
TriggeredBy: ● certbot.timer
Docs: file:///usr/share/doc/python-certbot-doc/html/index.html
https://certbot.eff.org/docs
systemctl list-timers --all
kmgadmin@nginx:~$ systemctl list-timers --all
NEXT LEFT LAST PASSED UNIT ACTIVATES
Mon 2025-08-18 11:50:00 UTC 9min Mon 2025-08-18 11:40:06 UTC 32ms ago sysstat-collect.timer sysstat-collect.service
Mon 2025-08-18 12:58:34 UTC 1h 18min Mon 2025-08-18 11:18:53 UTC 21min ago fwupd-refresh.timer fwupd-refresh.service
Mon 2025-08-18 14:32:53 UTC 2h 52min Sun 2025-08-17 14:32:53 UTC 21h ago update-notifier-download.timer update-notifier-download.service
Mon 2025-08-18 14:42:55 UTC 3h 2min Sun 2025-08-17 14:42:55 UTC 20h ago systemd-tmpfiles-clean.timer systemd-tmpfiles-clean.service
Mon 2025-08-18 17:02:01 UTC 5h 21min Mon 2025-08-18 11:08:32 UTC 31min ago motd-news.timer motd-news.service
Mon 2025-08-18 18:46:11 UTC 7h - - certbot.timer certbot.service
Mon 2025-08-18 22:41:05 UTC 11h Mon 2025-08-18 09:14:31 UTC 2h 25min ago apt-daily.timer apt-daily.service
Tue 2025-08-19 00:00:00 UTC 12h Mon 2025-08-18 00:00:17 UTC 11h ago dpkg-db-backup.timer dpkg-db-backup.service
Tue 2025-08-19 00:00:00 UTC 12h Mon 2025-08-18 00:00:17 UTC 11h ago logrotate.timer logrotate.service
Tue 2025-08-19 00:07:00 UTC 12h Mon 2025-08-18 00:07:17 UTC 11h ago sysstat-summary.timer sysstat-summary.service
Tue 2025-08-19 06:16:55 UTC 18h Mon 2025-08-18 06:57:47 UTC 4h 42min ago apt-daily-upgrade.timer apt-daily-upgrade.service
Tue 2025-08-19 09:39:11 UTC 21h Mon 2025-08-18 10:46:02 UTC 54min ago man-db.timer man-db.service
Sun 2025-08-24 03:10:19 UTC 5 days Sun 2025-08-17 03:10:56 UTC 1 day 8h ago e2scrub_all.timer e2scrub_all.service
Mon 2025-08-25 01:22:35 UTC 6 days Mon 2025-08-18 00:33:05 UTC 11h ago fstrim.timer fstrim.service
Mon 2025-08-25 18:57:40 UTC 1 week 0 days Mon 2025-08-18 00:38:53 UTC 11h ago update-notifier-motd.timer update-notifier-motd.service
- - - - apport-autoreport.timer apport-autoreport.service
- - - - snapd.snap-repair.timer snapd.snap-repair.service
- - - - ua-timer.timer ua-timer.service
18 timers listed.
Useful Resources
SSH Config File